Vulnerability Assessment, Penetration Testing
Comprehensive Cybersecurity, Confidentially Delivered.
Comprehensive Network Security Audits & Penetration Testing
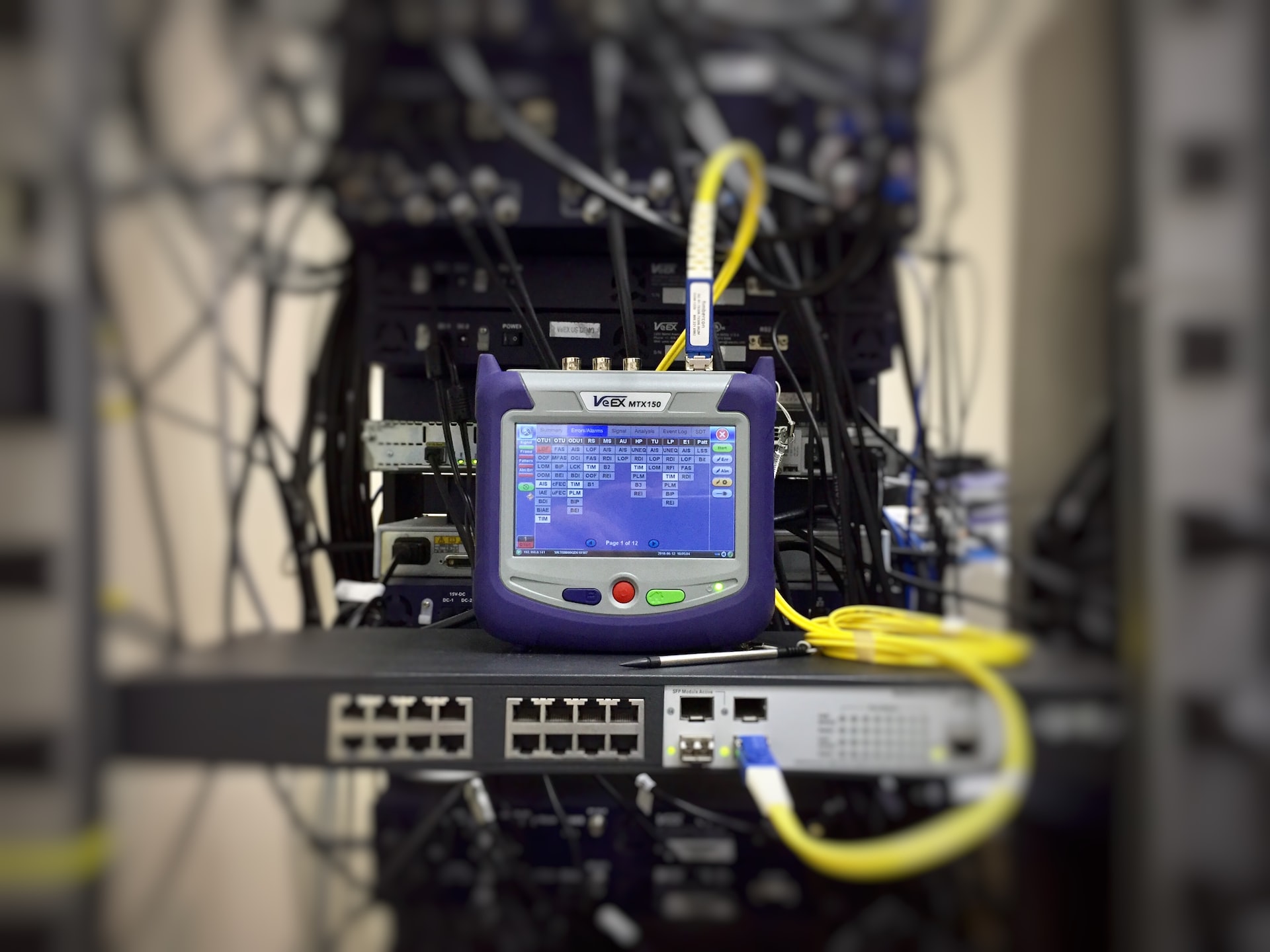
The increase in cyber attacks means there is an urgent need to be pro-active about security audits and prevention. At Plectrum, we know the severity of cyber attacks which is why we always offer a robust and periodic Network Vulnerability Assessment, Auditing and Penetration Testing to our clients. We carry out a systematic evaluation of your entire IT infrastructures. We evaluate system risk levels through detailed security audits; access known and unknown weaknesses in your operating systems, apps, and network devices to always keep you safe. Clients who engage our expertise on this can be assured of authenticity, thoroughness, and 100% confidentiality of their data assets.
Vulnerability Management and Scanning
Comprehensive threat management and vulnerability management services are essential to securing your organization. We proactively respond to threats and vulnerabilities, we created a unique vulnerability management program that blends advanced data sciences and orchestration technology with deep security skills for predicting vulnerability before it’s in your environment, and discovering and preventing exploitation of existing vulnerabilities. Our vulnerability management services are designed to identify security holes within an organization’s IT infrastructure, specifically related to cyber threats. Our vulnerability assessment services run a series of diagnostics on company devices, applications, and networks, and utilize this data to recommend areas for improvement based on urgency and scope.

Plectrum Advantage
Our experienced, highly Skilled team focuses on developing a personal relationship with our clients, learning about your business needs and how best to apply technology to solve problems and create new opportunities.
Service Features
Our plans include high-impact IT services to provide your company with an efficient, cost-effective, and responsive IT experience.
Complete coverage
Rest assured knowing that your IT systems are being monitored at all times to optimize performance, reduce downtime, prevent security attacks, and protect your data.
24/7 Help
Our support team provides rapid response to your organisation to ensure they remain secure and productive. Contact us via our support site or reach us by phone, email or our website .
Predictable budget
With our flexible monthly subscriptions, you’ll be able to accurately project your IT spend without any surprises.
Threat Management
Protect against cyber threats and unauthorized access by conducting security audits and deploying preventive measures.
Reporting
From ticket details and service performance to project status and invoicing, enjoy detailed reporting that keeps you updated and informed on every aspect of our engagement.
Threat Intelligence and Vulnerability Management
Effective security starts with a clear understanding of your vulnerabilities. We can help you gauge your strengths and weaknesses in a wide variety of scenarios, from facility security to executive protection. Not only do we bring decades of experience to our vulnerability management services, our leading experts can also help you anticipate potential sources of new threats.
What is Vulnerability Risk Management
Risk-based vulnerability management is a cybersecurity strategy in which organizations prioritize remediation of software vulnerabilities according to the risk they pose to the organization. A risk-based vulnerability management strategy has several components.
Common terms that are used when discussing cyber risks are vulnerabilities, exploits, and threats. It is necessary to understand the difference between these terms and what they mean in terms of risk and in terms of prioritizing what to do to keep your systems safer.
What is Vulnerability Risk Management
- A vulnerability is a weakness or flaw in the measures you take to secure an asset.
- An exploit is an attack that takes advantage of vulnerabilities.
- A threat is something that may or may not happen, but is anything that might exploit a vulnerability to breach security and potentially cause serious harm or damage.

Let's get started
Get started today by contacting one of our experienced consultants. We'll guide you step by step to modernize your IT, drive meaningful business outcomes, and achieve your goals.
Our Service
Vulnerability Assessment, Penetration Testing
The increase in cyber attacks means there is an urgent need to be pro-active about security audits and prevention. At Plectrum, we know the severity of cyber attacks which is why we always offer a robust and periodic Network Vulnerability Assessment, Auditing and Penetration Testing to our clients. We carry out a systematic evaluation of your entire IT infrastructures. We evaluate system risk levels through detailed security audits; access known and unknown weaknesses in your operating systems, apps, and network devices to always keep you safe. Clients who engage our expertise on this can be assured of authenticity, thoroughness, and 100% confidentiality of their data assets.
Vulnerability Management and Scanning
Comprehensive threat management and vulnerability management services are essential to securing your organization. We proactively respond to threats and vulnerabilities, we created a unique vulnerability management program that blends advanced data sciences and orchestration technology with deep security skills for predicting vulnerability before it’s in your environment, and discovering and preventing exploitation of existing vulnerabilities. Our vulnerability management services are designed to identify security holes within an organization’s IT infrastructure, specifically related to cyber threats. Our vulnerability assessment services run a series of diagnostics on company devices, applications, and networks, and utilize this data to recommend areas for improvement based on urgency and scope.










What We’re Offering
Vulnerability Assessment, Penetration Testing
Threat Intelligence and Vulnerability Management
Effective security starts with a clear understanding of your vulnerabilities. We can help you gauge your strengths and weaknesses in a wide variety of scenarios, from facility security to executive protection. Not only do we bring decades of experience to our vulnerability management services, our leading experts can also help you anticipate potential sources of new threats.
Risk-based vulnerability management is a cybersecurity strategy in which organizations prioritize remediation of software vulnerabilities according to the risk they pose to the organization. A risk-based vulnerability management strategy has several components.
Common terms that are used when discussing cyber risks are vulnerabilities, exploits, and threats. It is necessary to understand the difference between these terms and what they mean in terms of risk and in terms of prioritizing what to do to keep your systems safer.

What is Vulnerability Risk Management
A vulnerability is a weakness or flaw in the measures you take to secure an asset.
An exploit is an attack that takes advantage of vulnerabilities.
A threat is something that may or may not happen, but is anything that might exploit a vulnerability to breach security and potentially cause serious harm or damage.
Perfect solutions that business demands

Providing excellent technology solutions
We eagerly put in use new IT innovations
Active Clients
Projects Completed
Glorious Years
Professional team
We ensure the acceleration of productivity within your core organizational functions.
Contact
- hello@plectrumbusiness.com
© Copyright 2025. All Right reserved. Plectrum Business Solution



