Don’t know how to solve your Cyber Security situation
Fighting threats is hard enough without the battle you fight every day. The battle to keep your head above water while managing security solutions.
Lets help you Solve the Complexity
What Are Cybersecurity Services?
Cyber security solutions are your organisation’s protection against unauthorized or criminal use of electronic data, and cybersecurity services are the overarching processes put in place to achieve this security and protect against common cyber threats. These common threats that our cybersecurity Solution can help with includes Malware, Ransomware, Phishing, Distributed denial of service (DDoS) attacks.

Take a look at our Cyber Security Solution Offering
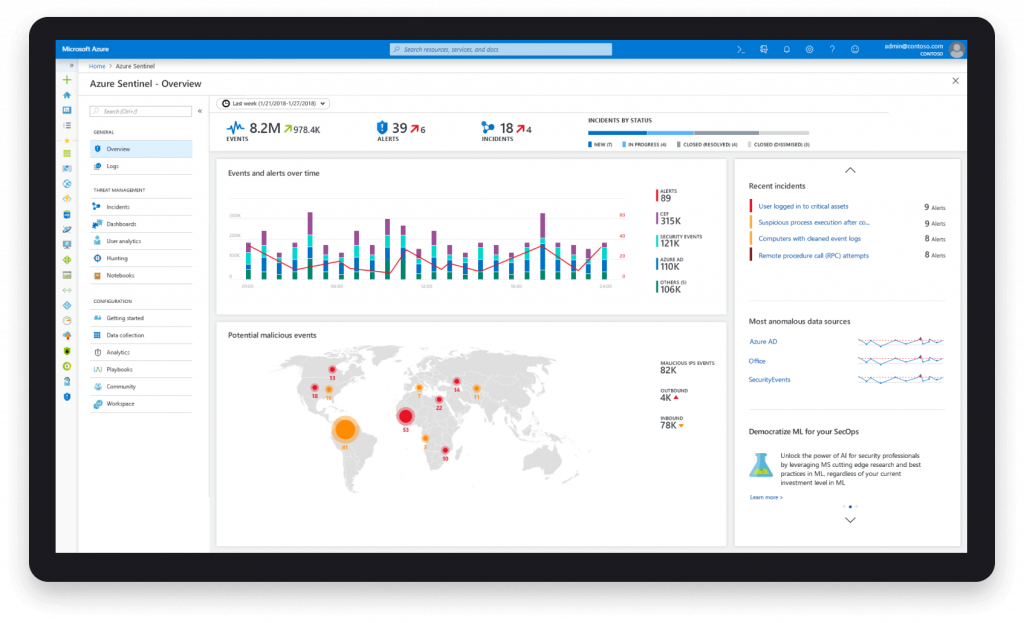
Azure Sentinel
Build next-generation security operations with cloud and AI
See and stop threats before they cause harm, with SIEM reinvented for a modern world. Microsoft Sentinel is your birds-eye view across the enterprise. Put the cloud and large-scale intelligence from decades of Microsoft security experience to work. Make your threat detection and response smarter and faster with artificial intelligence (AI). Eliminate security infrastructure setup and maintenance and elastically scale to meet your security needs—while reducing costs as much as 48 percent compared to traditional SIEMs.
Limitless cloud speed and scale
Invest in security, not infrastructure setup and maintenance, with the first cloud-native SIEM from a major cloud provider. Never let a storage limit or a query limit prevent you from protecting your enterprise. Start using Microsoft Sentinel immediately, automatically scale to meet your organisational needs and pay for only the resources you need. As a cloud-native SIEM, Microsoft Sentinel is 48 percent less expensive and 67 percent faster to deploy than legacy on-premises SIEMs.
A match for all your tools
Connect to and collect data from all your sources including users, applications, servers and devices running on-premises or in any cloud. Integrate with existing tools, whether business applications, other security products or homegrown tools and use your own machine-learning models. Optimise for your needs by bringing your own insights, tailored detections, machine learning models and threat intelligence.